Encrypt and Decrypt A Text File with AWS KMS and EC2 Instance
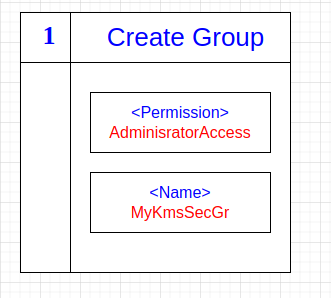
In this post, I will show, how to encrypt a text file with Amazon Key Management Service (KMS) and EC2 Instance. First of all, we need a Security Group with AdministrationAccess. Let's create our Security Group.
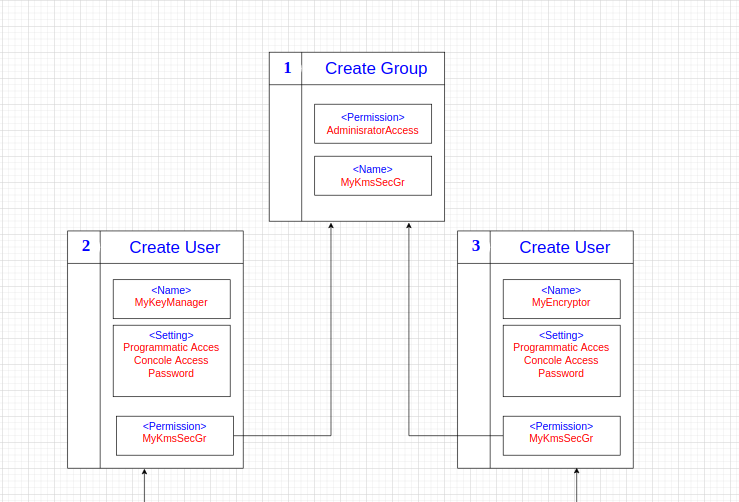
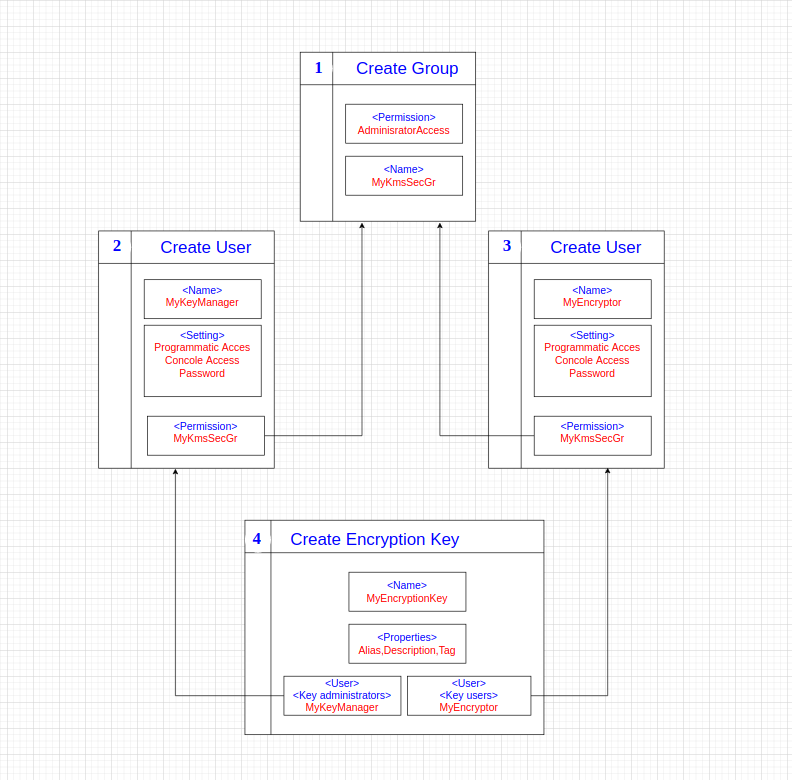
Instead of showing all the operations on the AWS Console step by step, I will proceed using diagrams.
Creating Security Group
Creating Users
We need a user called EncryptorUser who will do encryption and decryption operations. And we must copy Access Key Id and Secret Access Key this user to a file or download .csv file, we will use this credentials later. We also need another user called KeyManager who perform KMS management operation. We assign these two users to the group with AdministratorAccess we just created.
Creating Encryption Keys
After creating the user and adding it to the relevant group, we will generate our encryption key. It should be noted that AWS KMS is not a global service, it is a regional service. This means a key in one region is not used to encrypt the data in another region.
Create and Launch EC2 Instance
Now we are ready to create our EC2 Instance. Our EC2 Instance will have the following properties.
- Amazon Linux AM
- t2-micro (free tier eligible)
- Leave other properties as default
- Create a group that have HTTP and SSH permission or choose an existing group
In the last step, we must download the .pem file of our secret keys. With this .pem file we will connect to our EC2 Instance. And we copy the public ipv4 address of our instance to the clipboard.
Connect EC2 Instance
We are ready now to connect our EC2 instance. We are opening bash on our computer.
First we give write access to our .pem file.
chmod 400 key-pair-for-kms-ec2-instance.pem
fatih@fatih-thinkpad:~/Downloads$ ssh ec2-user@<ip-address-your-instance> -i key-pair-for-kms-ec2-instance.pem
__| __|_ )
_| ( / Amazon Linux 2 AMI
___|\___|___|
https://aws.amazon.com/amazon-linux-2/
6 package(s) needed for security, out of 16 available
Run "sudo yum update" to apply all updates.
[ec2-user@<ip-address-your-instance> ~]$
Encryption Operations
We are now connected to EC2 Instance. Then we give root privilege. And we create a text we want to encrypt.
sudo su
echo "Data to be encrypted" > my-secret-data.txt
Now we must configure our AWS account for encryption operation. We copied the Access Key Id and Secret Access Key of the MyEncryptor user to a file. We will now use them. We run the following command.
aws configure
We set our AWS account and
[root@ip-your-instance ec2-user]# aws configure
AWS Access Key ID: ***************
AWS Secret Access Key: *************
Default region name: eu-west-2
Default output format [None]:
[root@ip-your-instance ec2-user]#
We are ready to encrypt and decrypt our secret files. With the following commands, we can perform all encryption and decryption operations. Only we must replace the YOURKEY field with our Encryption Key Id.
aws kms encrypt --key-id YOURKEY --plaintext fileb://my-secret-data.txt --output text --query CiphertextBlob | base64 --decode > encrypteddata.txt
aws kms decrypt --ciphertext-blob fileb://encrypteddata.txt --output text --query Plaintext | base64 --decode > decrypteddata.txt
aws kms re-encrypt --destination-key-id YOURKEY --ciphertext-blob fileb://encrypteddata.txt | base64 > newencrypteddata.txt